Quick Facts
- Category: Finance & Crypto
- Published: 2026-05-04 04:16:50
- How Azure’s Integrated HSM Builds Trust Through Open Hardware
- Declining U.S. Birth Rate Triggers New Political Debate Over Family Supports
- Building in Healthcare: FDA Approval, Fundraising, and Team Motivation – Insights from BioticsAI CEO
- Understanding the 2024 Supreme Court Decision on Voting Rights and Racial Gerrymandering: A Guide to the Louisiana v. Callais Case
- Python 3.14 Release Candidate 1: What You Need to Know
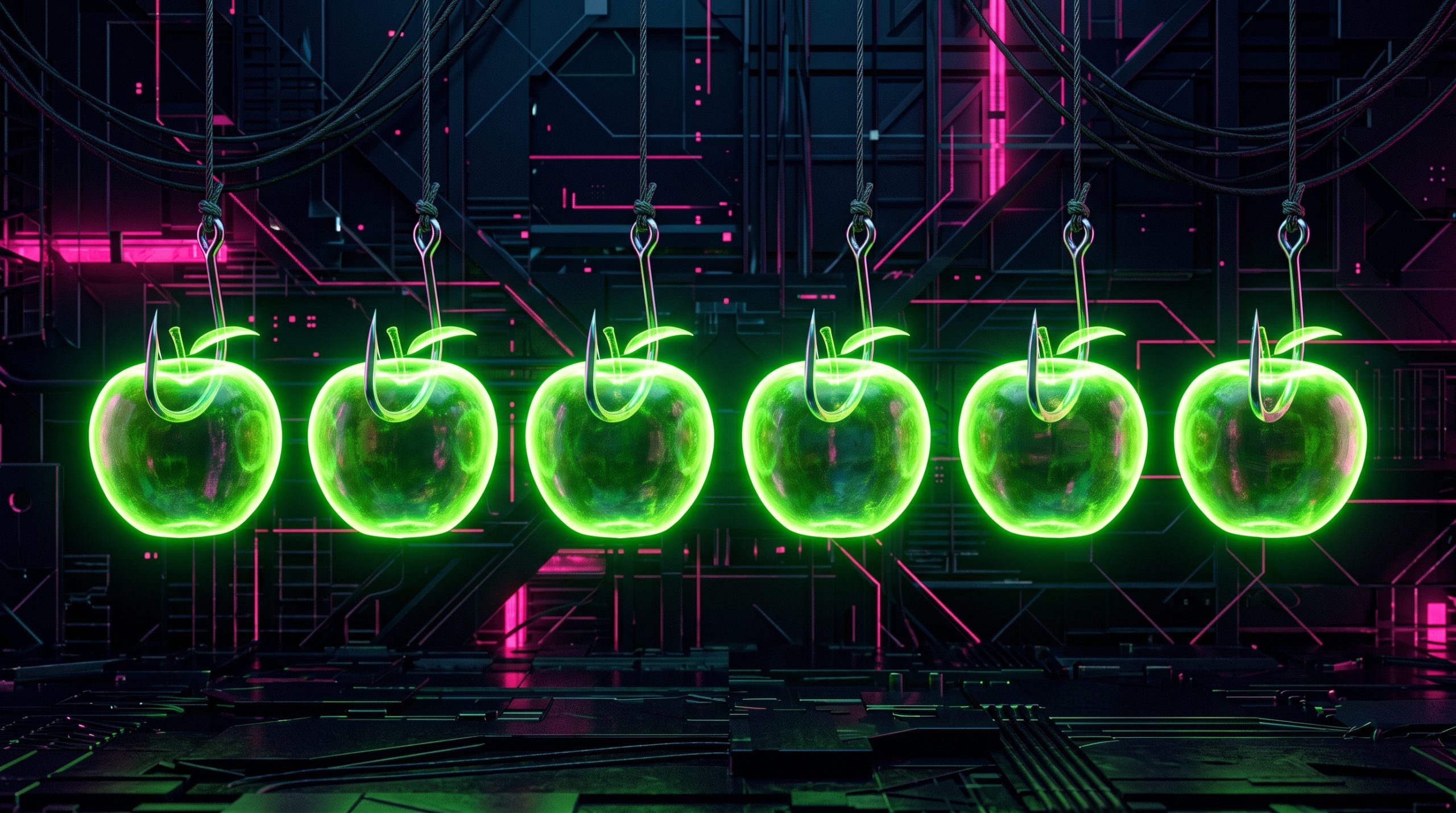
In March 2026, cybersecurity researchers uncovered a sophisticated campaign involving more than twenty phishing apps in the Apple App Store, all designed to steal cryptocurrency wallets. These apps masqueraded as popular crypto wallets but secretly redirected users to malicious browser pages that distributed trojanized versions of legitimate software. Here are seven critical things you need to know about this growing threat.
1. The Discovery: A Hidden Campaign Exposed
Investigators first noticed a wave of suspicious apps topping search results in the Chinese App Store in early 2026. These apps appeared under names like MetaMask, Ledger, Trust Wallet, and Coinbase, but closer inspection revealed they were cleverly crafted fakes. Metadata from the malware indicated the operation had been active since at least fall 2025, flying under the radar for months. By the time researchers identified 26 phishing apps, several had already been downloaded thousands of times. The team promptly reported their findings to Apple, leading to the removal of many malicious apps.
2. The Modus Operandi: Fake Apps That Look Real
Each fake app mimicked the official wallet's icon and name, often with intentional typos—a practice called typosquatting. Once launched, the app redirected users to a webpage that looked nearly identical to the App Store. There, victims were tricked into downloading a trojanized version of the legitimate wallet. This infected version was specifically engineered to hijack recovery phrases and private keys. Some apps even included functional stubs—like a simple game or calculator—to make the app appear authentic and avoid immediate suspicion.
3. The Regional Targeting: Why China Is Ground Zero
The campaign primarily targeted Chinese users due to regional restrictions. Many official crypto wallet apps are unavailable in the Chinese App Store because of local regulations, effectively creating a vacuum. Scammers exploited this gap by flooding search results with fake alternatives. Promotional banners within these apps falsely claimed the official wallet was unavailable and urged users to download through the app itself. This geographic focus allowed attackers to operate with less chance of global detection, while preying on users desperate for access to legitimate services.
4. The Technical Trick: Typosquatting and Stubs
Attackers employed a two-pronged technical strategy: typosquatting and stubs. Typosquatting meant using names that differed by a single letter or simple swap (e.g., "Metamask" instead of "MetaMask") to slip past App Store filters. The stubs were functional placeholders—a calculator, a task planner—that made the app appear benign. These elements not only evaded initial review but also gave the app a legitimate feel after installation. Only after launch did the malicious redirection trigger, making it difficult for casual users to detect the scam.
5. The Stolen Data: Recovery Phrases and Private Keys
The infected apps were designed with one primary goal: stealing cryptocurrency. Once a victim entered their recovery phrase or private key into the trojanized wallet interface, the data was immediately sent to attackers. This allowed them to drain any associated wallets. The targeted wallets included major names like MetaMask, Coinbase, Trust Wallet, TokenPocket, Bitpie, imToken, and OneKey. Because recovery phrases provide full access to funds, victims often lose everything within minutes, with little hope of recovery.

6. The Historical Precedent: A Resurgence of an Old Threat
This isn't the first time such a scheme has appeared. In 2022, ESET researchers identified compromised crypto wallets distributed through phishing sites. That earlier campaign abused iOS provisioning profiles to install malware, successfully stealing recovery phrases from the same hot wallets. Four years later, the technique has evolved: now using new malicious modules, updated injection methods, and App Store distribution. The 2026 version is more sophisticated, but the core attack remains the same—a reminder that cybercriminals adapt traditional scams to new platforms.
7. The Detection and Removal: What Apple Did
Kaspersky products detect this threat under the names HEUR:Trojan-PSW.IphoneOS.FakeWallet.* and HEUR:Trojan.IphoneOS.FakeWallet.*. After reporting the 26 identified apps, Apple removed several from the store. However, researchers also found similar apps that showed no active phishing functionality but appeared linked to the same threat actors. These apps likely contained dormant code waiting to be activated in a future update. This suggests that simply removing known malicious apps may not be enough—users must remain vigilant against future variants.
Protect yourself by downloading apps only from official developer pages, double-checking app names for typos, and never entering recovery phrases into any third-party interface. The FakeWallet campaign is a stark warning that even trusted platforms like the App Store can harbor sophisticated scams. Stay informed, stay cautious, and always verify before you trust.